What SEBI's Cybersecurity Framework Actually Means for Your Broking Firm
"The SEBI cyber audit is next quarter."
"We're fine. We have policies in place."
"What about the dealers working from home? Their devices, the session logs from those terminals?"
A pause.
"We'll figure it out before then."
Walk into any broking firm's IT or compliance meeting today, and some version of this conversation is happening. The problem is that "we'll figure it out" is not a posture that survives a SEBI cyber audit. Not anymore.
What SEBI actually put on paper
In August 2024, SEBI issued the Cybersecurity and Cyber Resilience Framework, a consolidated directive that replaced every previous cybersecurity circular across all regulated entities. This is not a tightened version of older guidelines. It replaces every previous cybersecurity circular across every category of regulated entity, stockbrokers, AMCs, depositories, RTAs, portfolio managers, clearing corporations, and brings them under one consolidated framework for the first time.
The CSCRF covers every SEBI-regulated entity. It is graded by size and operational scope, but there is no carve-out that exempts smaller firms from the fundamental controls. Compliance deadlines have been extended multiple times following requests from regulated entities, with the most recent extension pushing the deadline for most REs to August 31, 2025. Market Infrastructure Institutions, KYC Registration Agencies, and Qualified RTAs were held to earlier deadlines given their systemic importance.
Every extension SEBI has granted came with a clear message: this is procedural accommodation, not a softening of enforcement intent.
The controls that actually matter on the ground
The CSCRF is built around five cyber resilience goals: Anticipate, Withstand, Contain, Recover, and Evolve. Beneath that structure sit operational mandates that most broking firms and AMCs are underprepared for.
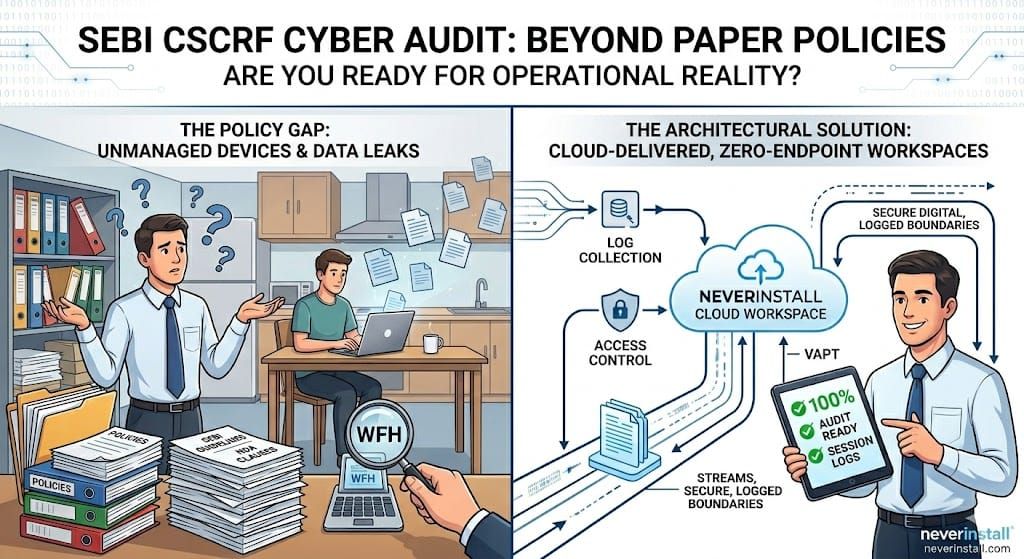
It is not the governance requirements that catch firms off guard. Those get documented. The gap is almost always in the operational layer.
CSCRF mandates authentication and access policies with comprehensive log collection and retention across all critical systems. Every access event must be logged. Every session must be auditable and producible on demand. For Qualified Regulated Entities and Market Infrastructure Institutions, VAPT must be conducted half-yearly. High-severity vulnerabilities identified during VAPT must be remediated within one week of report submission.
The framework explicitly requires endpoint security solutions with proper authentication and authorization mechanisms. Network segmentation to restrict access to sensitive data is mandatory, not optional. And critically, regulated entities are solely responsible for ensuring that third-party vendors meet CSCRF requirements.
Not partially responsible. Solely responsible.
Your vendor's compliance gap is your audit finding. The regulator will not distinguish between the two.
The WFH problem SEBI already put on record
This is not theoretical risk. In 2022, after allowing brokers and fund managers to operate from home during the pandemic, SEBI reversed course and issued an internal circular requiring broking houses and mutual fund houses to return to office operations. The stated reason was documented surveillance lapses that emerged when dealers operated from unregistered locations, creating monitoring gaps that compromised oversight of trading activity.
SEBI's position was unambiguous: when a dealer operates a trading terminal from a location that is not a registered branch office, the firm's ability to maintain required surveillance is structurally compromised.
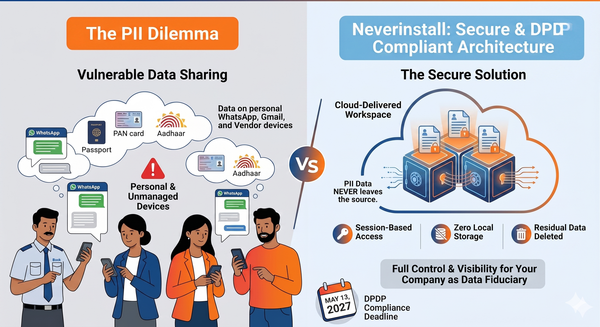
The CSCRF formalizes that concern into mandatory technical controls. When a dealer, relationship manager, or back-office operator accesses trading systems or client data from a personal device at an unregistered location, it creates an audit trail problem that no policy document can paper over. Session data may not be centrally captured. Endpoint controls may be unenforceable on hardware the firm does not manage.
For a firm under SEBI audit, this is not a minor gap. It is a structural compliance failure.
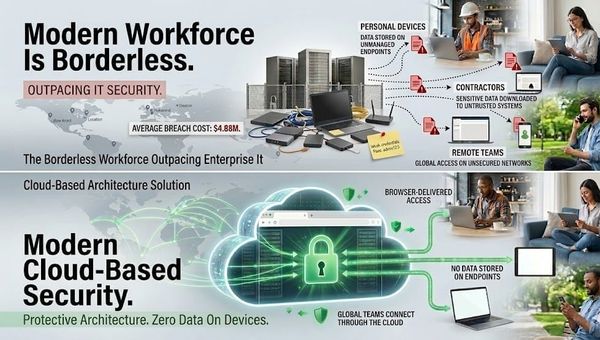
Why the standard IT stack does not close this
Most broking firms and AMCs have VPNs, firewalls, and some form of endpoint detection. What they have not solved is the underlying data path problem. When remote access is configured to allow local caching, or when employees and contractors access systems from personal devices, the audit trail breaks the moment data leaves the controlled environment.
A dealer working remotely downloads a client portfolio summary for a review call. That file now exists on a personal laptop. CSCRF's requirements for log retention and data access management cannot be satisfied from that point forward because you have no visibility into what happens to that file after the download.
Device policies help on managed hardware. They do not reach personal devices. And across India's broking ecosystem, a significant portion of remote access happens on hardware the firm does not own or control.
This is an architecture problem, not a policy problem
The reflex in most compliance teams is to solve this with better documentation. Tighter device use policies. More detailed access protocols. Stronger NDA clauses with vendors. These have marginal value.
None of them change the underlying architecture, which is one where sensitive data can travel from your controlled environment to an endpoint you do not manage. The audit trail gap does not exist because people are non-compliant. It exists because the architecture makes the gap structurally inevitable.
Policies govern behavior. Architecture governs what is structurally possible.
The question worth asking is not how to better manage data after it reaches an unmanaged device. The question is whether it needs to reach that device at all.
The architectural answer SEBI's framework is pointing toward
The firms that come out of SEBI cyber audits cleanly are not the ones with the most thorough policy manuals. They are the ones where the architecture itself enforces the controls the framework requires.
In a cloud desktop model, the dealer or analyst accesses their workspace through a session that lives entirely within controlled, auditable infrastructure. The compute happens in the cloud. Nothing downloads to the local device. The session is logged end to end. When the session closes, there is no residual data on the endpoint, whether the device is managed or personal.
This directly satisfies CSCRF's requirements for log collection, access management, and endpoint security. The audit trail is complete because the session never left your perimeter. The endpoint risk is eliminated because nothing reached the endpoint. Remote and hybrid operations become possible without creating the surveillance gap SEBI has consistently penalized.
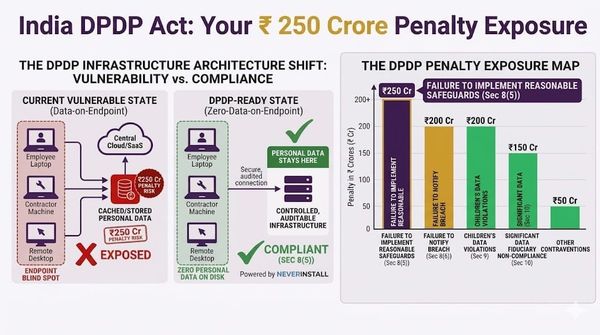
For regulated entities managing client data under both CSCRF and India's DPDP Act, this architecture addresses both compliance obligations through the same infrastructure decision.
What your auditor will actually ask
SEBI's CSCRF audit is conducted by CERT-In empanelled auditors. They will ask for evidence of implemented controls, not stated policies. Log retention records showing complete session capture. Access control documentation. Endpoint security implementation proof. Incident response plan test results.
The firms that treat CSCRF as a documentation exercise will find the gaps very quickly under audit. The firms that treat it as an infrastructure question will not have gaps to find.
There is a meaningful difference between a firm that can say "we have an endpoint policy" and a firm that can say "our architecture makes local data retention structurally impossible." One of those answers ends the conversation. The other one starts a longer one.
Where Neverinstall fits
Neverinstall delivers cloud-based workspaces built for environments where auditability, access control, and zero endpoint data residency are non-negotiable. For SEBI-regulated entities, this means remote and hybrid teams operate within fully logged, centrally controlled sessions where no data touches unmanaged devices and no audit trail gaps exist.
It is not a compliance layer added on top of existing infrastructure. It is different infrastructure that makes compliance structurally achievable.
The question your compliance team needs to answer
When your SEBI auditor asks for complete access logs from your last quarter's remote sessions, every terminal, every device, every data access event, what will you hand them?
The firms that have already answered that question at the architectural level are the ones that will not be scrambling to answer it under audit pressure.
Learn More
Explore how Neverinstall helps SEBI-regulated entities meet CSCRF requirements through cloud-delivered, zero-endpoint workspaces: neverinstall.com
Related Reads