What Happens to Your Data When a Contractor Leaves?
"Access revoked?"
"Yes."
"And the data he accessed last week — the customer records?"
"He was on his own laptop. We don't manage his device."
"So where is that data right now? Have we erased it?"
Silence.
That silence is one of the most expensive sounds in enterprise security. And it happens more often than anyone on your board wants to know. A contractor finishes their engagement. Access gets revoked. A box gets ticked on the offboarding checklist. And somewhere on a personal device in another city, your customer data, invoices, or product roadmap sit quietly in a downloads folder indefinitely.
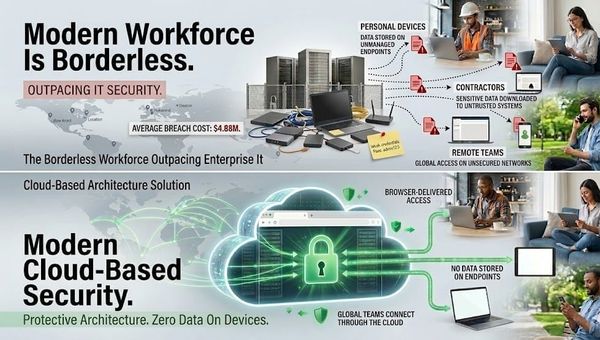
The risk no one says out loud
Modern enterprises don't run on full-time employees alone. They run on a contractor economy - vendor engineers, freelance developers, consultants, outsourced sales agents, dealers, agency teams. This is especially true across India's fast-scaling digital-native companies and the FSI sector, where agility demands flexible talent models.
Many of these contractors work on personal laptops. They connect over VPN, access internal systems, pull files they need to do their job, and occasionally - entirely routinely - download things locally. Customer datasets. Financial models. Design files. API logs. Code repositories.
When the engagement ends, your IT team revokes their credentials. That part works correctly. What it doesn't do is reach into their device and remove the data they've already touched. That data stays. There is no technical mechanism in a standard offboarding process that changes this.
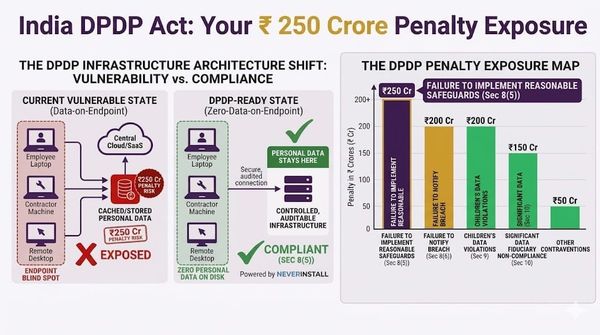
India's DPDP Act puts this squarely on you
Here is where it becomes a legal problem, not just a security one.
Under India's Digital Personal Data Protection Act, 2023 - notified by MeitY [Ministry of Electronics and Information Technology] on November 13, 2025 and with full compliance required by May 13, 2027 - if your organization collects or processes personal data of Indian citizens, you are a Data Fiduciary.
Section 8(1) of the Act states plainly: a Data Fiduciary is responsible for compliance "irrespective of any agreement to the contrary" in respect of any processing undertaken by it or on its behalf by a Data Processor. If a contractor functioning as a Data Processor retains personal data after their engagement ends, the regulatory exposure sits with your organization. Not theirs. Yours.
Section 8(5) further mandates that you implement reasonable security safeguards to prevent personal data breaches. Failure to do so carries a penalty of up to ₹250 crore. That figure doesn't require an actual breach to trigger - inadequate safeguards alone can constitute a violation.
Your NDA with the contractor doesn't change this. Your offboarding checklist doesn't change this. The DPDP Act's language is deliberate: accountability cannot be outsourced. A vendor's negligence is treated as your breach.
Why your existing controls don't solve it
This is the part worth being honest about.
VPN access revocation blocks the contractor from connecting to your systems going forward. It does nothing about data already downloaded. Access revocation removes their login credentials. It doesn't touch their local storage. Device policies only apply to managed devices - and most contractors aren't using yours. NDAs create legal deterrents but require you to prove what data was retained and how it was used, which is nearly impossible without endpoint visibility you don't have.
Screenshots were taken. Files were cached. Repositories were cloned. Exports were run. Every one of those data paths bypassed your controls the moment the data left your perimeter and landed on an unmanaged device.
This is the uncomfortable truth: the standard enterprise offboarding process was designed for full-time employees on managed hardware. It was never designed for the contractor economy that now touches your most sensitive data.
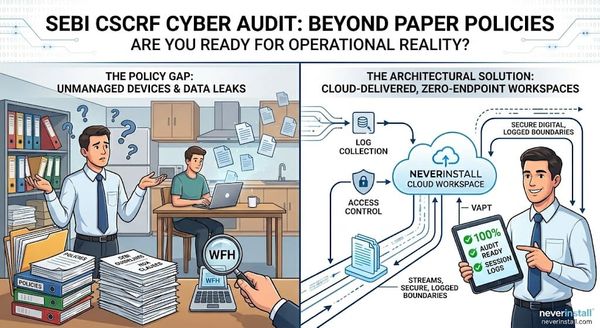
This is an architecture problem, not a process problem
The instinct when something like this surfaces is to tighten the process. Stronger NDAs. More detailed offboarding checklists. Better access segmentation policies. These things have marginal value.
What they don't change is the underlying architecture - one where data can travel from your environment to an endpoint you don't control. As long as that data path exists, the risk exists. Policies govern behavior. Architecture governs what's structurally possible.
The question isn't how to better manage data after it reaches an endpoint. The question is whether it needs to reach an endpoint at all.
Zero data on endpoint: the architectural answer
The principle is straightforward. A contractor should be able to work with sensitive data without ever possessing it.
In a zero-data-on-endpoint model, the contractor gets a cloud-delivered workspace. They can write code, access dashboards, analyze files, run queries - all within a session that lives entirely inside your infrastructure. Nothing is downloaded locally. Nothing is cached on their device. The compute, the storage, and the application state all remain within your perimeter.
When the engagement ends, access is revoked and the session terminates. There is nothing to recover from the contractor's device, because nothing was ever there. The audit trail is complete. The offboarding is architecturally clean.
Your DPDP obligations aren't satisfied by policy;they're satisfied by design.
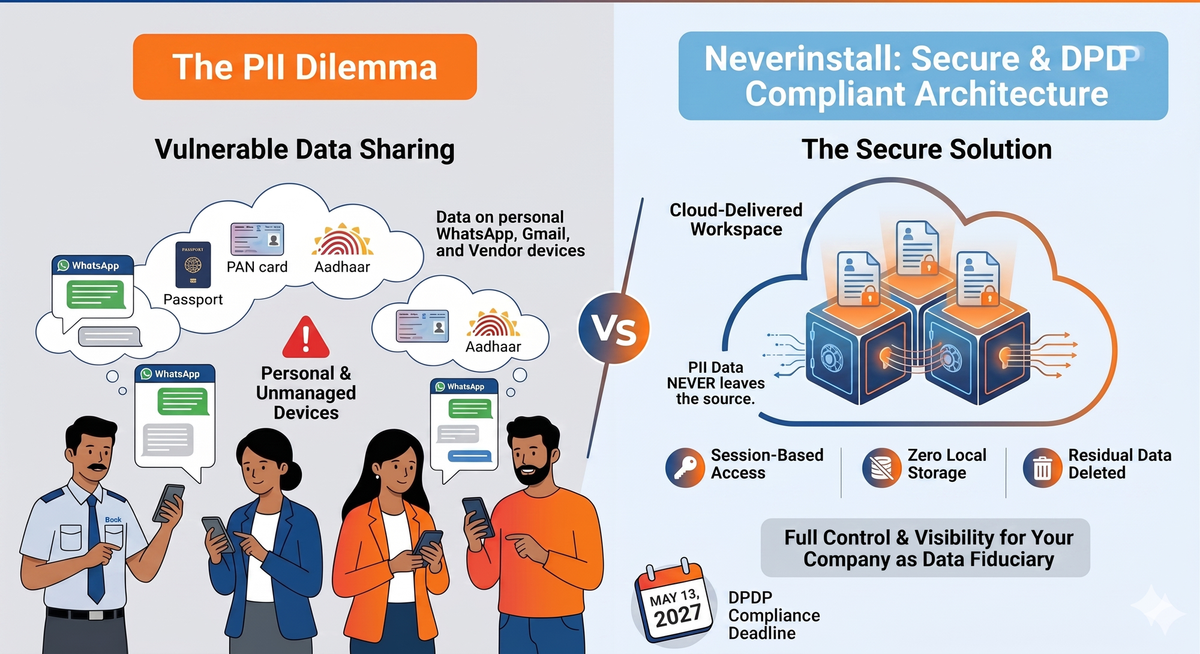
What this looks like in practice
A fintech onboards a vendor engineering team for a payments integration project. They need access to production logs containing transaction metadata. In a standard setup, those logs get cloned locally during debugging. In a cloud workspace model, the engineers work directly in the session - the logs never leave your environment, and when the contract ends, so does access to every byte they worked with.
A consultant is brought in to analyze user cohort data. In a standard setup, they export a CSV and work locally. In a cloud workspace model, the analysis happens inside a session you provision and control. When the engagement closes, the data stays with you.
The security outcome isn't dependent on the contractor's behavior. It's dependent on what the architecture makes possible - and in a zero-endpoint model, local retention simply isn't possible.
Why this matters right now
According to IBM's 2024 Cost of a Data Breach Report, the average cost of a data breach in India reached an all-time high of INR 195 million - a 39% increase since 2020. IBM That figure covers breach costs alone, before any DPDP regulatory penalty is applied. Stack a ₹250 crore fine on top of a ₹19.5 crore breach response bill, and you're looking at an event that is existential for most mid-size Indian enterprises.
The contractor economy isn't shrinking. Remote and hybrid work has normalized vendor access to sensitive systems. Compliance timelines under the DPDP Act are running. The organizations that respond to this architecturally — not with better paperwork — will have a structurally defensible position come 2027.
Where Neverinstall fits
Neverinstall provides cloud-delivered workspaces built on the principle that work happens in the cloud, and data stays there. Contractors access applications and environments through sessions that live entirely within your infrastructure — no local downloads, no persistent storage on unmanaged devices, no data residency outside your control. Access revocation is instant and complete.
It's not a layer on top of existing architecture. It's a different architecture.
The question worth sitting with
When a contractor's access is revoked, your systems are protected.
But what about everything they touched before that?
The organizations asking that question now and answering it at the architectural level are the ones that won't be answering regulators later.
Learn More
If you're rethinking how contractors access sensitive data inside your organization, start with the architecture.
Explore how Neverinstall delivers secure, zero-endpoint workspaces for enterprise teams: neverinstall.com
Related Reads