The India DPDP Act and Your IT Infrastructure — What Every CIO Needs to Know
Most Indian CIOs are treating the DPDP Act like a legal problem.
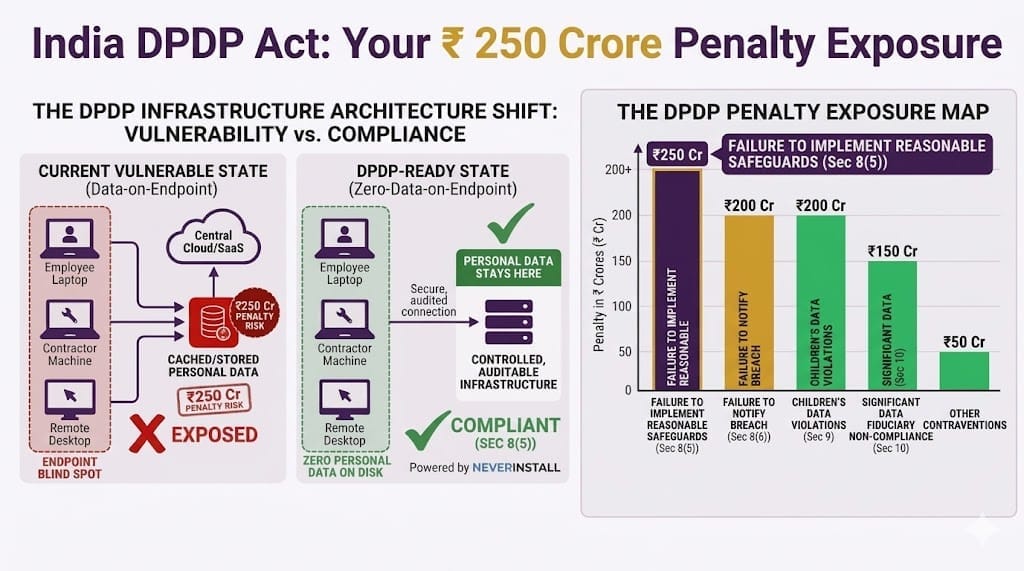
It's actually an infrastructure problem. If your endpoints are storing personal data, even temporarily, you are potentially exposed to a penalty of up to ₹250 crore per breach.
What Section 8 Actually Demands From You
The Digital Personal Data Protection Act, 2023, backed by the DPDP Rules, 2025, is India's definitive data privacy law. Full compliance is required by May 14, 2027 — but the infrastructure work starts now.
Under the Act, if your organisation collects, processes, or stores digital personal data of Indian citizens, you are a Data Fiduciary. Size and turnover are irrelevant.
There are 3 obligations every CIO must internalise:
- Section 8(1): You are liable for compliance irrespective of any agreement to the contrary. If your cloud vendor, SaaS tool, or contractor causes a breach — the law treats it as YOUR breach.
- Section 8(5): You must implement reasonable security safeguards to prevent personal data breaches. Penalty for failure: up to ₹250 crore — even if no actual harm occurs.
- Section 8(6): You must notify the Data Protection Board and affected individuals of any breach. Failure to notify carries a separate penalty of up to ₹200 crore.
The Board doesn't need to prove a breach happened. It needs to show that your safeguards weren't reasonable. The distinction matters enormously.
The Penalty Exposure Map
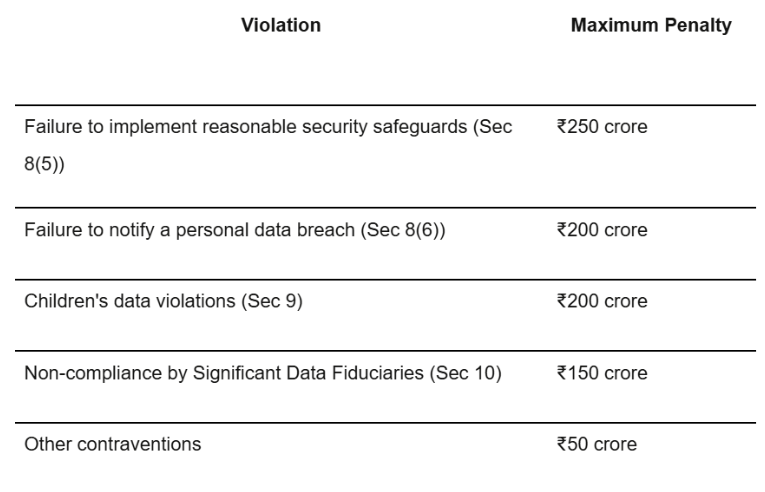
These are per contravention — not annual caps. Multiple failures stack. In extreme cases, the Central Government can direct blocking of public access to a non-compliant organization's services entirely.
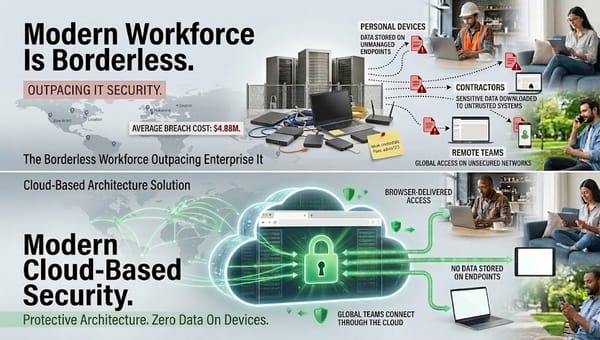
The Endpoint Blind Spot
Most compliance conversations stop at privacy notices and consent flows. They miss the biggest exposure: your endpoints.
Every device accessing personal data — employee laptops, contractor machines, remote desktops syncing to local storage — is a potential breach point. Under the DPDP Act, that data is under your control, regardless of where the device physically sits.
Scenarios your company is likely dealing with right now (whether you acknowledge it or not):
- Hybrid employees retaining customer information on unmanaged devices. Think of an insurance agent who took pictures of a customer's PAN or Aadhaar and forgot to delete it from their personal device
- Contractors with their own hardware accessing your internal systems
- SaaS tools caching personal data at the endpoint level
The average cost of a data breach in India is already approximately ₹22 crores— before any regulatory penalty. Add a ₹250 crore DPDP fine, and you're looking at a potentially business-ending event for most mid-size Indian companies.
Most of this exposure lives on endpoints that IT doesn't fully control.
What "Reasonable Safeguards" Means in Practice
Rule 6 of the DPDP Rules sets the minimum floor:
- Encryption at rest and in transit
- Least-privilege access controls
- Patch and vulnerability management
- Breach notification mechanisms
- Security obligations contractually bound to all Data Processors
But "shall include" signals a floor, not a ceiling. Regulators will benchmark against ISO 27001, NIST, and CERT-IN guidelines. If your endpoint posture doesn't hold up against those standards, your safeguards argument is weak.
The Architectural Fix: Zero Data on Endpoint
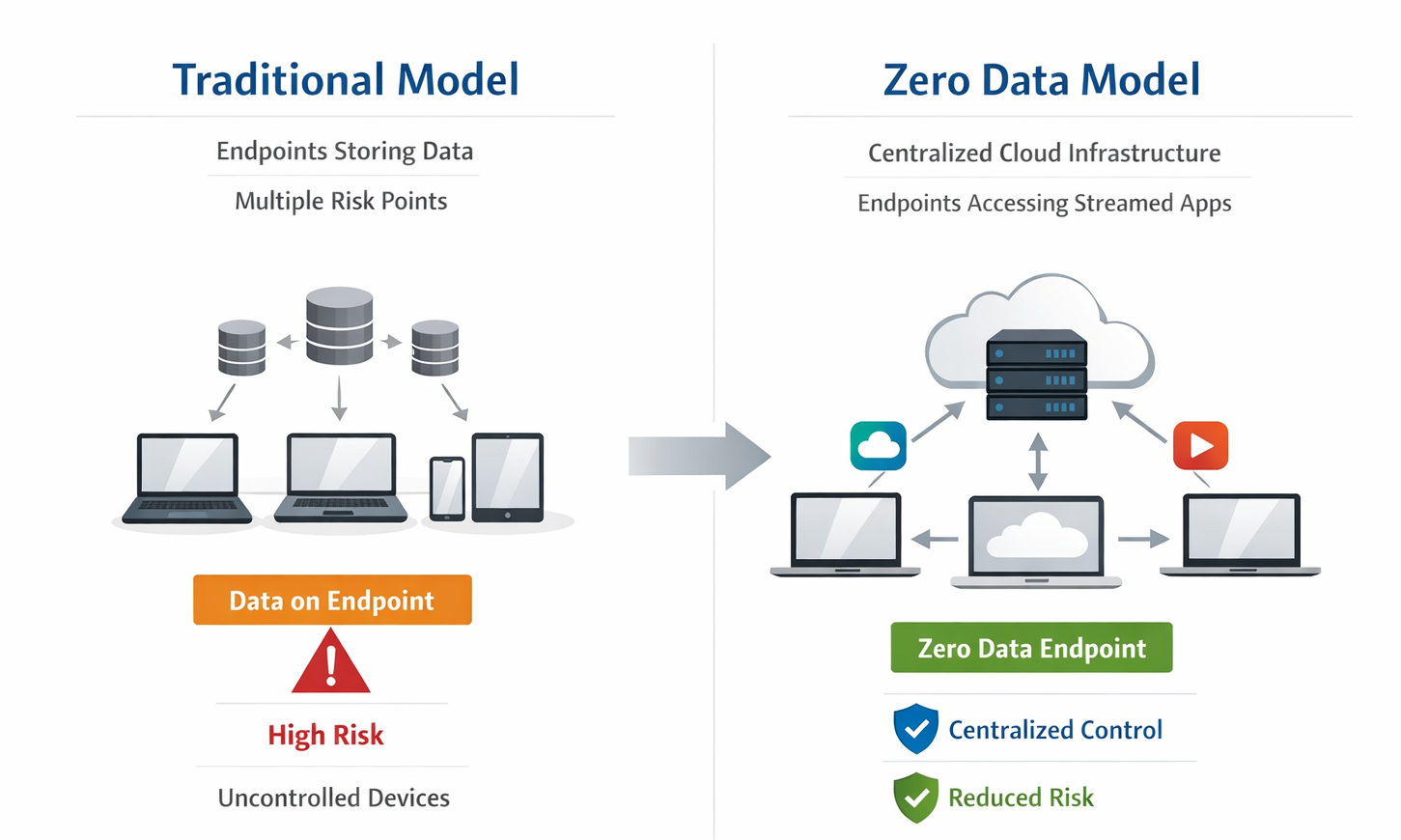
The most defensible DPDP posture isn't layering more tools onto data-heavy endpoints. It's removing data from the endpoints entirely.
Zero-data-on-endpoint architecture means:
- Applications stream to devices; nothing writes to local storage
- Sessions terminate cleanly — no residual data
- A lost or stolen laptop is a compliance non-event
- Contractor and vendor access is scoped, auditable, and reversible
This is the principle behind Neverinstall — cloud-delivered application access that keeps personal data inside controlled, auditable infrastructure. Under this model, Section 8(5) compliance becomes structural, not policy-dependent.
Three Actions for CIOs Right Now
1. Map endpoint data exposure first. Identify which devices are accessing personal data, what's being cached or downloaded locally. This is your breach surface. You cannot protect what you haven't mapped.
2. Audit your vendor contracts. Every 3rd party processing Indian personal data needs a Data Protection Addendum. Start with the five vendors touching your most sensitive data. Section 8(1) vicarious liability applies the moment their contract is silent on DPDP.
3. Plan the architectural shift now. Zero-data-on-endpoint takes time to implement. Get the data map and contracts right first — then eliminate endpoint exposure systematically.
The Bottom Line
The DPDP Act is the most significant shift in India's IT governance landscape since the IT Act of 2000. Companies treating it as a legal 'task' will likely face a compliance crisis by May 2027. Companies treating it as infrastructure rethink will not.
Section 8 is your liability. The endpoint is your exposure. ₹250 crore is the cost of getting it wrong.
See how Neverinstall eliminates endpoint data risk →
#DPDPAct #DataPrivacyIndia #CIOIndia #CISOIndia #ITGovernance #DataProtection #EndpointSecurity #ZeroTrust #Neverinstall #DataFiduciary #IndiaCompliance #DataSecurity2026