The End of the Support Ticket:

Why Regulated Enterprises Must Redesign the Endpoint
For nearly three decades, enterprise IT has been built on an uncomfortable assumption: endpoints are fragile, and support is the unavoidable cost of doing business.
We budget for it.
We staff for it.
We normalize it.
Operating system corruption. Driver conflicts. Broken updates. “It worked yesterday.” VPN failures. Local configuration drift. These incidents are treated as routine rather than structural signals.
In regulated industries, the burden is heavier still. Add disk encryption enforcement, endpoint detection agents, certificate chains, and compliance tooling — all competing for control of the same operating system. The result is predictable: highly skilled engineers spending their time repairing machines instead of designing systems.
This is not a people problem.
It is not a training problem.
It is not a tooling problem.
It is an architectural problem.
And architecture always wins.
A structural transition is now underway inside financial services, healthcare, defense, and government-adjacent enterprises. Not a cosmetic tool upgrade, but a redesign of where compute, control, and trust live. The support ticket, as an operating model, is quietly approaching obsolescence.
The Real Cost of Endpoint Entropy
Most enterprises underestimate what endpoint instability truly costs.
When fully loaded — salaries, tooling, escalation paths, facilities, and lost productivity — a single support ticket in a large organization typically costs between $70 and $150. This excludes the more damaging impacts: delayed onboarding, broken developer environments, and operational distraction.
What generates the majority of tickets is remarkably consistent:
- OS corruption
- Patch regressions
- Dependency conflicts
- Security agent collisions
- VPN failures
- Local misconfiguration
These are not business failures. They are side effects of distributing compute and control to thousands of unmanaged environments.
In regulated sectors, the risk compounds. Audit findings increasingly point to endpoint drift. Shadow IT emerges when provisioning is slow. Data exposure occurs through unmanaged devices. Compliance tooling interferes with engineering workflows. The modern enterprise stack is hardened in the data center and cloud, but remains fragile at the edge.
We built zero-trust networks and left the endpoint as a trust sink.
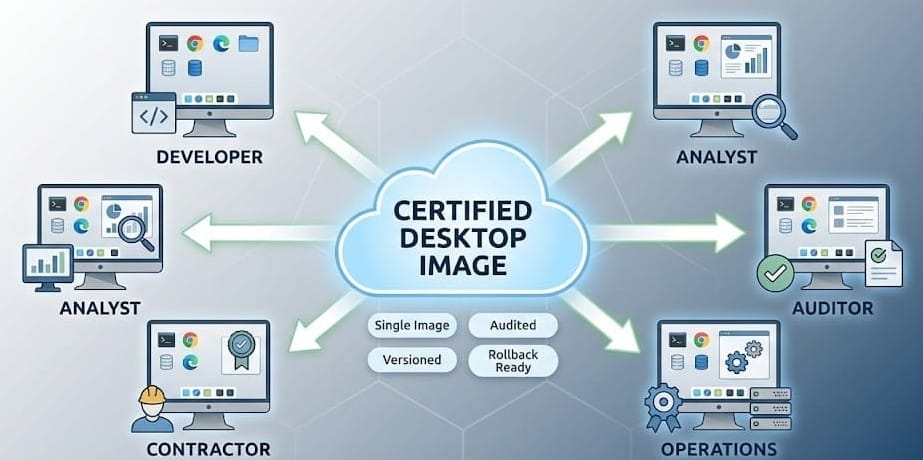
Standardization Is Not a Cost Play. It Is a Control Strategy
Centralizing the desktop is often framed as an efficiency initiative. That framing is incomplete.
It is, at its core, a governance strategy.
When the user environment becomes a centrally managed artifact, the logic of control changes. Every user runs the same hardened image. Every application is validated once. Every update is deliberate. Every rollback is immediate.
Failure modes collapse. OS corruption becomes irrelevant. Malware loses persistence. Patch failures become reversible. Configuration drift disappears.
This is not virtualization for convenience. It is policy enforcement through design.
Instead of managing ten thousand machines, infrastructure teams manage one environment. Instead of certifying laptops, they certify images. Instead of repairing endpoints, they govern systems.
This marks the transition from operational IT to strategic IT.
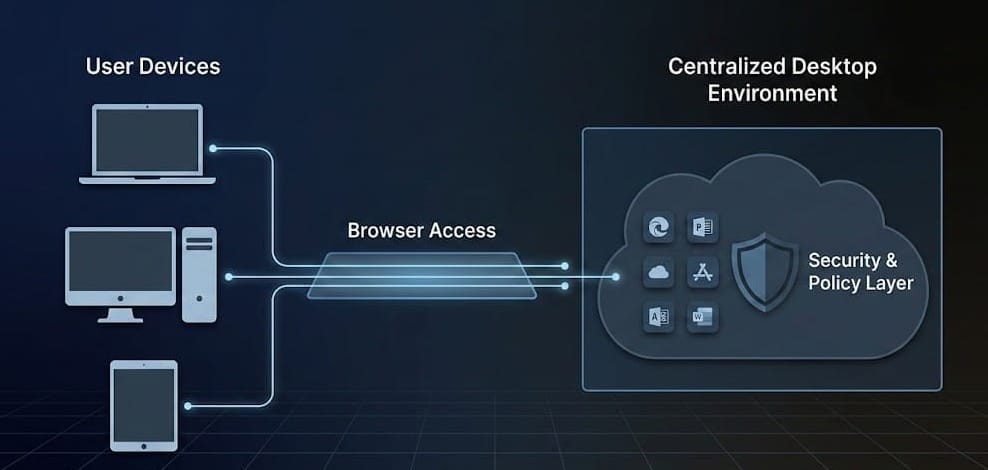
The Browser as the New Trust Boundary
Historically, enterprises anchored trust to the device, the network, and the perimeter. None of these remain reliable.
Remote work is permanent. Contractors are ubiquitous. BYOD is unavoidable. VPNs are no longer a boundary; they are a workaround layered on top of an eroded model.
The modern trust boundary is the session.
In a browser-based desktop architecture, identity, environment, and application collapse into a single control plane. Data never persists on the device. Clipboard, file transfer, and printing can be governed. Session behavior becomes observable. Zero-trust becomes enforceable at the point of interaction rather than the point of connection.
From a security perspective, the endpoint becomes disposable. The attack surface centralizes. Audit trails become deterministic.
From an infrastructure perspective, the model eliminates device imaging pipelines, local software lifecycles, and hardware dependencies. The device becomes a window, not a workplace.
This is not a technical novelty. It is a philosophical shift: access replaces ownership.
Onboarding as an Architectural Signal
The quality of an infrastructure model is most visible on day one.
Traditional onboarding is a choreography of procurement, imaging, shipping, VPN provisioning, certificate setup, application installation, and security agent troubleshooting. Under ideal conditions, this takes weeks.
In a centralized, browser-based desktop model, onboarding reduces to identity creation, access assignment, and environment instantiation. Time collapses from weeks to minutes.
This is not an HR convenience story. It is a risk story.
Slow onboarding produces personal devices, unapproved cloud tools, data outside policy, and invisible workflows. Fast onboarding enforces standardized environments, compliant toolchains, controlled access, and immediate visibility.
Speed is not a luxury. It is a security control.
Compliance Scales with Images, Not Devices
Auditors do not fear breaches as much as they fear ambiguity. The most expensive failures are not incidents; they are findings.
Centralized desktop environments invert the audit model. Instead of certifying thousands of laptops across multiple operating systems and driver combinations, enterprises certify a single environment, a defined update cadence, and a consistent security envelope.
When auditors ask how data exfiltration is controlled, how applications are whitelisted, or how developer tooling is governed, the answer is architectural, not procedural.
Compliance becomes an operational state rather than an episodic panic.
Why This Is Not “VDI All Over Again”
Virtual desktops are often associated with latency, complex brokers, VPN dependencies, and on-prem bottlenecks. That model belonged to a different era.
Browser-native desktop platforms remove client agents, VPN tunnels, and local configuration entirely. They operate like cloud services rather than infrastructure projects.
The control plane shifts from managing machines to managing sessions and images. Sessions are ephemeral. Images are versioned. Environments are reproducible.
That is modern infrastructure language.
Why Platforms Like Neverinstall Matter in This Transition
Not because they are faster.
Not because they are cheaper.
But because they align infrastructure with modern risk models.
A browser-based desktop platform delivers centralized compute, controlled environments, no local data footprint, identity-first access, and audit-ready logging. The result is predictable:
Security teams gain visibility.
Compliance teams gain certainty.
Infrastructure teams gain leverage.
CIOs gain predictability.
This is not a feature upgrade. It is an operating model change.
The Death of the Support Ticket Is a Governance Story
Support tickets are not the enemy. They are the symptom.
They represent environmental inconsistency, uncontrolled state, local failure modes, and human-scaled repair loops. A well-designed system should not require constant human intervention.
Regulated enterprises already understand this principle in data centers, networks, and cloud workloads. The endpoint is simply the last unmanaged frontier.
Centralizing the desktop completes the control plane.
Closing Thought
Every generation of infrastructure reaches a moment when its operating model becomes the bottleneck.
Mainframes gave way to servers.
Servers gave way to cloud.
Now endpoints must give way to environments.
The enterprises that recognize this early will move faster, audit cleaner, breach less, and spend less on repair. Those that do not will continue hiring engineers to fight physics.
The support ticket is not dying because tools improved.
It is dying because architecture matured.
And architecture always wins.
