The Distributed Employee IT Nightmare

Or: “I am paying a salary for no work.”
The distributed workforce was supposed to be a strategic breakthrough. Global hiring. Flexible operations. Resilience by design. In boardrooms, it still sounds compelling.
In IT operations, it feels very different.
What was marketed as freedom has become a logistics-heavy, risk-amplifying delivery problem. Not because remote work is flawed, but because the way we deliver IT to remote workers has not fundamentally changed.
We stretched a device-centric model built for office corridors across continents.
It is now breaking under its own weight.
The Illusion of Modernization
Many enterprises believe they have modernized workforce IT because they use cloud apps, VPNs, and endpoint management tools. But look at the operating reality:
- Work still begins with a physical shipment
- Security still depends on what that shipment does
- Productivity still waits for delivery
We modernized software.
We did not modernize distribution.
That mismatch is now visible in four operational fault lines.
1. The Onboarding Drag
Traditional flow:
Offer accepted → Laptop ordered → Imaging → Shipping → Customs → First login.
Operational reality:
For international or cross-border hires, it routinely takes two to three weeks before a usable device arrives.
During that time:
- Salary is paid
- Access is partially provisioned
- Managers wait
- Output is zero
This is not a people problem.
It is a delivery model failure.
No manufacturing leader would accept a three-week delay before a production line could start. Yet we accept it for knowledge workers.
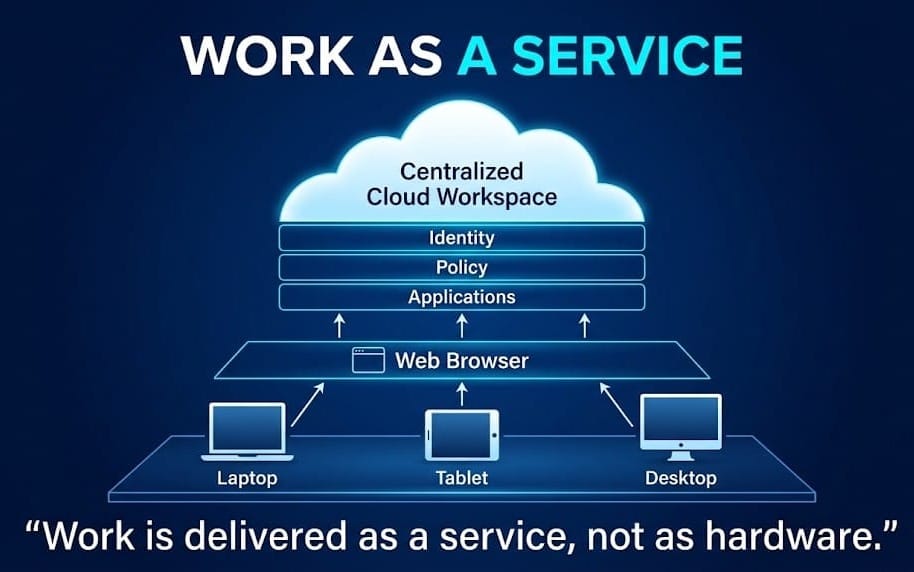
In a centralized workspace model:
- Identity is created
- Access is granted
- A browser becomes the terminal
Work begins in minutes, not weeks.
Onboarding shifts from logistics to security.
That is not a convenience feature. It is a structural change.
2. The Retrieval Gap
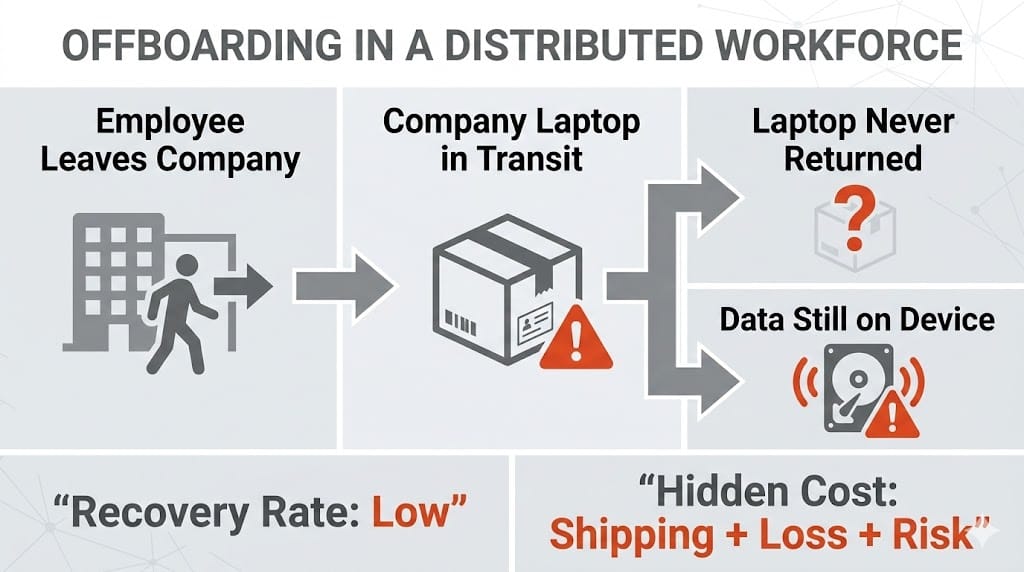
Offboarding exposes the second weakness of device-based IT.
Devices do not reliably return.
Addresses change. Couriers fail. Customs holds packages. Assets disappear. Insurance claims begin. Data risk remains unresolved.
Across distributed organizations, recovery rates are consistently low. The true cost of retrieval is not the hardware. It is:
- Shipping
- Handling
- Compliance checks
- Time
- Loss exposure
By the time a device is back and verified, the recovery cost often approaches or exceeds half its original value.
When the workspace lives in the cloud:
- Nothing is shipped
- Nothing is retrieved
- Nothing is sanitized
Access is revoked.
The asset never leaves.
This reverses a long-standing assumption: offboarding can be cheaper than onboarding.
That is an architectural outcome, not a procedural one.
3. The Helpdesk Hamster Wheel
Distributed endpoints multiply operational variance.
A single driver failure, OS corruption, or patch conflict now requires:
- Remote diagnosis
- Screen sharing
- Rebuild attempts
- Or physical return
Support economics are well known:
- Tier 1 is inexpensive
- Tier 3 is not
- Escalation is disruptive
But the deeper issue is not ticket cost.
It is unpredictability.
Some users recover in minutes.
Others lose days.
That variability is unacceptable in regulated or revenue-sensitive environments.
With a centralized workspace:
- The device becomes irrelevant
- The environment becomes reproducible
- State becomes disposable
You do not repair sessions.
You replace them.
This is how resilient systems are designed everywhere else in IT. End-user computing should not be the exception.
4. The Shadow Security Reality
Security leaders already know what happens next.
When onboarding is slow or support is unreliable, employees do what they must to work:
- Personal laptops
- Local file downloads
- Browser-stored credentials
- Unmanaged software
Not out of defiance. Out of necessity.
This is where compliance erodes:
- Data leaves controlled environments
- Audit trails fragment
- Forensics weaken
- Risk shifts to user behavior
A browser-delivered workspace creates structural separation:
- Data stays in the cloud
- Identity governs access
- Policy travels with the session
- Audit becomes inherent
Security becomes architectural rather than aspirational.
Instead of trusting behavior, the system makes unsafe behavior impossible.

Stop Managing Boxes
Most enterprises still treat laptops as the workplace.
They budget them. Track them. Ship them. Insure them. Repair them.
But endpoints are no longer the workplace.
They are viewing terminals.
The actual workplace consists of:
- Identity
- Applications
- Data
- Policy
- Observability
Those belong centrally.
The question is no longer whether desktops can run in the cloud. That problem has been solved.
The real decision is philosophical:
Will IT continue to manage fragile physical objects,
or will it deliver work as a service?
This transition already happened to:
- Servers
- Storage
- Networks
- Telephony
End-user computing is simply late.
Strategic Impact (Not Feature Lists)
From an executive lens, centralized workspaces change three operating dimensions.
Financial
- Hardware refresh cycles slow
- Logistics shrink
- Support variance drops
- Cost per user stabilizes
Spending becomes predictable operating cost rather than episodic capital shock.
That is not accounting theater.
It is risk reduction.
Operational
- Onboarding becomes access provisioning
- Offboarding becomes access revocation
- Support becomes image management
- Security becomes design
IT stops acting as a shipping department and starts operating as a service platform.
Human
Distributed talent is no longer gated by hardware delivery.
Productivity begins on day one, not day twenty-one.
That is the difference between remote work as an idea and remote work as a system.
The Real Transformation
The future of work is not about:
- Faster couriers
- Better packaging
- Lighter laptops
- Smarter tracking
It is about streaming the workplace.
Just as we stream:
- Video
- Compute
- Databases
- Development environments
The desktop itself becomes a service.
When that happens:
- Geography becomes irrelevant
- Devices become interchangeable
- Logistics disappear
What remains is:
- Policy
- Identity
- Experience
Which is exactly where CIOs should operate.
Bonus Effect: Hardware Life Extension
A side effect often overlooked:
When the workspace is centralized, endpoint requirements collapse.
Organizations can:
- Reuse older devices
- Support secure BYOD
- Delay refresh cycles
- Reduce e-waste
- Flatten capital spending
A browser becomes the new thin client.
Thin clients have always won in long-term economics.
They just needed modern networks to work properly.
Final Thought
Distributed work is not the nightmare.
Delivering it with physical-first thinking is.
The organizations that will outperform over the next decade will not be those with the best laptops.
They will be the ones who realized:
Work is software. Not hardware.
Stop managing boxes.
Start delivering workplaces.
When the desktop moves to the cloud, the logistics nightmare ends — and the talent dream finally becomes operational reality.
