The Borderless Workforce Is Scaling Faster Than Your IT
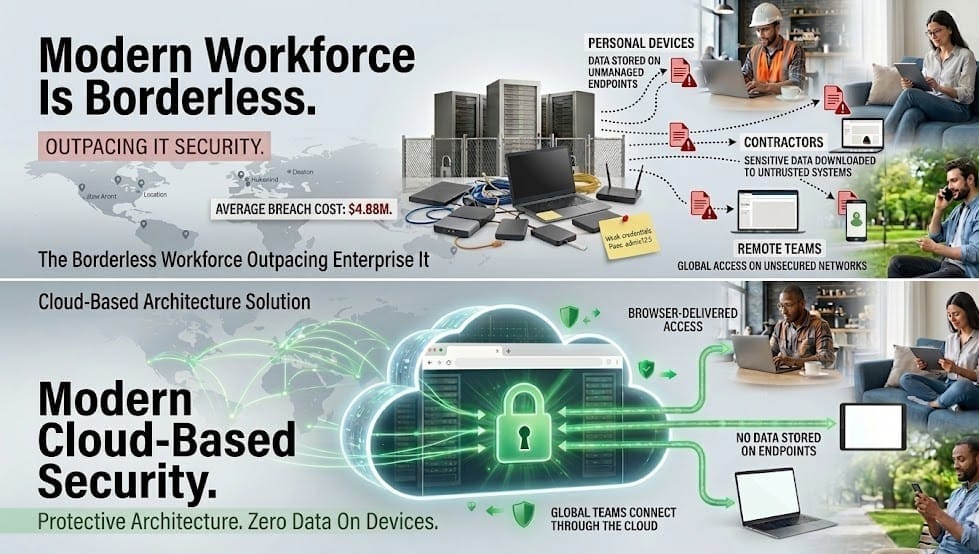
Work is no longer tied to offices.
But most IT infrastructure still is.
This is the defining tension of modern enterprise IT - and most organizations are losing it quietly, one unmanaged endpoint at a time.
The Shift That Snuck Up on Enterprise IT
It didn't happen in a single quarter. There was no board resolution, no change management plan. The workforce simply evolved - and left the org chart behind.
Today, 64 million Americans freelance - 38% of the entire U.S. workforce, contributing $1.27 trillion to the economy annually (Upwork Freelance Forward 2023). They aren't outliers or stopgaps. They are senior engineers, product designers, security consultants, and data scientists - working across time zones, on personal devices, accessing your systems through whatever connection is available.
This is the borderless workforce. And it is only accelerating.
The question every CTO, CIO, and Head of IT must answer today is not whether their teams are distributed. They already are. The real question is whether your infrastructure was built for this reality - or for the one that ended five years ago.
What "Borderless" Actually Means at Scale
Borderless workforce is often discussed conceptually. But at scale, it becomes an operational reality.
Your workforce today is not a single homogenous group of full-time employees on company-issued laptops behind a managed firewall. It is a fluid, layered ecosystem: full-time employees, contractors, freelancers, offshore developers, agency partners - each with different device profiles, different locations, and different levels of IT visibility.
When workers are offered flexible work arrangements, 87% of them take it - across all demographics and industries (McKinsey American Opportunity Survey, 2022, n=25,000). This is not a preference. It is an expectation. Companies that cannot accommodate it lose the talent competition before it begins.
And the trajectory only steepens. By 2027, 86.5 million Americans are projected to be freelancing - surpassing 50% of the U.S. workforce (Statista, 2024). At that scale, "the contractor" is no longer an edge case in your IT policy. The contractor is your workforce.
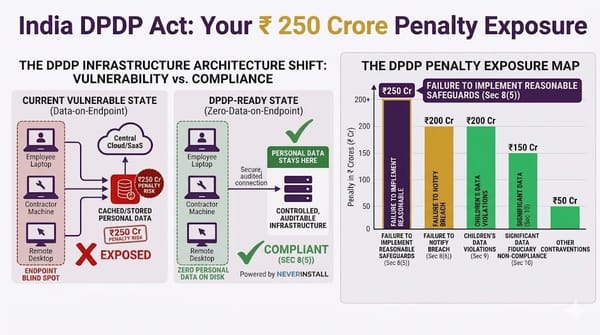
The Hidden Risk: Every Endpoint Is a Potential Exit Point
Here is what keeps security leaders awake - not the sophisticated nation-state attack, but the mundane workflow that happens every day:
- A freelance developer clones a production repository to their personal MacBook
- A contractor downloads a client dataset "just to work offline this weekend"
- A sales hire exports the full CRM on their last day before offboarding
None of these require malicious intent. They are ordinary, habitual behaviors - on devices IT has never touched, never enrolled, and cannot monitor.
The financial consequences of this exposure are well-documented. The global average cost of a data breach reached $4.88 million in 2024 - a 10% increase from the prior year and the largest single-year jump since the pandemic (IBM Cost of a Data Breach Report 2024). Stolen or compromised credentials were the #1 attack vector, accounting for 16% of all breaches - and took an average of 292 days to identify and contain. That is nearly ten months of active exposure.
70% of breached organizations reported significant or very significant operational disruption. The breach rarely announces itself. It compounds quietly, across unmanaged endpoints, until it cannot be ignored.
Why Traditional IT Architecture Fails Here
The architecture most enterprises are running today was designed for a different operating model: fixed offices, company-owned hardware, a defined perimeter.
Against a borderless workforce, every pillar of that model fails:
VPNs create the illusion of perimeter security while doing nothing to prevent local data storage, file downloads, or endpoint exfiltration once a user is authenticated.
Traditional VDI was never designed for contractor-scale flexibility. It is expensive to provision, operationally heavy to maintain, and falls apart the moment you try to scale it across hundreds of external collaborators.
Endpoint security agents require managed device enrollment - the exact condition that freelancers, contractors, and BYOD users cannot meet by definition.
The result is not a security gap. It is a security architecture that is structurally incompatible with the workforce you are already running.
The Borderless Workforce Infrastructure Stack
IT-ready infrastructure for a borderless workforce is not a product category. It is an architectural posture - built around a single non-negotiable principle: data never touches the endpoint.
This is not future architecture. It is available infrastructure, deployable today. The organizations moving fastest are already running it.
What Fast-Growing Companies Are Seeing
When infrastructure matches the operating model ,the results show up immediately - not as security metrics, but as business outcomes.
Hiring velocity increases. When onboarding a contractor no longer requires device enrollment, VPN provisioning, or IT ticket queues, time-to-productivity drops from days to hours. You hire the best candidate - in Lagos, Tallinn, or São Paulo - and they are operational within the hour.
The global talent pool opens completely. Device requirements and geographic proximity are no longer constraints. Your senior infrastructure engineer can be anywhere. Your design team can span four continents. IT infrastructure stops being a bottleneck to talent strategy.
Security risk decreases as the team scales. In a zero-data endpoint model, every new user added to the system does not add a new attack surface. Their device is irrelevant to your security posture. Access is controlled centrally; data stays in the cloud.
Offboarding becomes instantaneous. When a contractor's engagement ends, access is revoked at the identity layer. There is no device to retrieve, no local data to audit, no lingering credentials to rotate. The exit is clean by architecture.
CIO Readiness Checklist
Six questions to assess your infrastructure's fitness for a borderless workforce:
✔ Can contractors access your environment from an unmanaged personal device securely?
✔ Is sensitive data ever stored — even temporarily — on a local drive?
✔ Can you revoke all access from an offboarded contractor in under 60 seconds?
✔ Do you have session-level visibility into what every external user is doing right now?
✔ Is your security posture device-dependent or identity-dependent?
✔ Can you onboard a new contractor in a different country without an IT ticket?
If any answer gives you pause, the gap is architectural - not a policy problem, not a tooling problem.
How to Begin the Architectural Shift
This is not a rip-and-replace exercise. It is a phased migration towards an infrastructure model that matches the workforce you are operating today.
Step 1 : Audit current endpoint exposure. Map every active user - employee and contractor - against device type, enrollment status, and data access level. Understand your actual attack surface, not your assumed one.
Step 2 : Prioritize highest-risk access groups. Contractors with production system access, remote developers, and teams handling sensitive customer data represent the critical path. Start there.
Step 3 : Migrate critical workloads to cloud compute. Development environments, data tools, and business applications should run server-side. The laptop becomes a display - not a data store.
Step 4 : Deploy zero-data endpoint architecture. Ensure no session - regardless of user type or device - can result in local data storage, unauthorized download, or persistent access after offboarding.
Conclusion
By 2027, freelancers will make up the majority of the U.S. workforce. The contractors, remote hires, and distributed teams your organization depends on today are not a temporary accommodation. They are the permanent operating model.
The infrastructure question is not whether to adapt. It is how much longer adaptation can be deferred.
The workforce is already borderless. The only question is whether your IT is ready for it.
See how Neverinstall enables borderless, secure infrastructure for fast-growing teams → Explore Neverinstall