Stop Shipping Laptops: The Hidden Bottleneck in Scaling Regulated Workforces

Enterprises rarely fail to scale because they cannot hire. More often, they struggle because they cannot onboard.
In regulated sectors such as logistics, finance, healthcare, legal services, and government, the gap between hiring a contractor and enabling productive work is often measured in weeks. The constraint is rarely policy or identity governance. It is hardware.
Procure. Image. Ship. Track. Replace. Recover. Reimage.
This device lifecycle once aligned with traditional enterprise computing. Today, it conflicts with the distributed and project-driven structure of the modern workforce.
The issue is not remote work.
The issue is device-centric security.
The False Economy of Hardware-Based Onboarding
Enterprises frequently justify laptop provisioning in the name of security and compliance. The reasoning appears straightforward:
- Controlled endpoint
- Preconfigured system image
- Enforced security policies
- Known hardware supply chain
In practice, this model introduces structural inefficiencies.
Time-to-productivity declines.
A short-term contract that requires weeks of device provisioning immediately erodes engagement value.
Logistics becomes an IT dependency.
Courier delays, customs processes, device failures, and return cycles transform hardware shipping into a project risk factor.
Risk shifts rather than disappears.
Once a laptop leaves corporate custody, control becomes partially contractual. Physical loss, unmanaged software, and local malware remain outside the enterprise security perimeter.
More hardware does not necessarily produce more control.
In many cases, it simply expands the potential attack surface.

Why Contractors Expose Infrastructure Weaknesses
Contract workers rarely break infrastructure. They reveal its inefficiencies.
Permanent employees justify fixed assets. Contractors expose their operational rigidity.
A contractor typically requires:
- Immediate system access
- Limited operational scope
- Strict data containment
- Rapid access revocation
Traditional VDI and endpoint architectures were designed for long-term employees with predictable lifecycles. When applied to transient workforces, they often produce:
- Over-provisioned environments
- Excess licensing costs
- Fragile VPN dependencies
- Disproportionate IT support overhead
In regulated industries, the complexity increases. Compliance obligations—such as auditability, data residency, and access governance—become harder to enforce when infrastructure relies on distributed hardware endpoints.
What once appeared operationally manageable increasingly reveals itself as a structural design flaw.
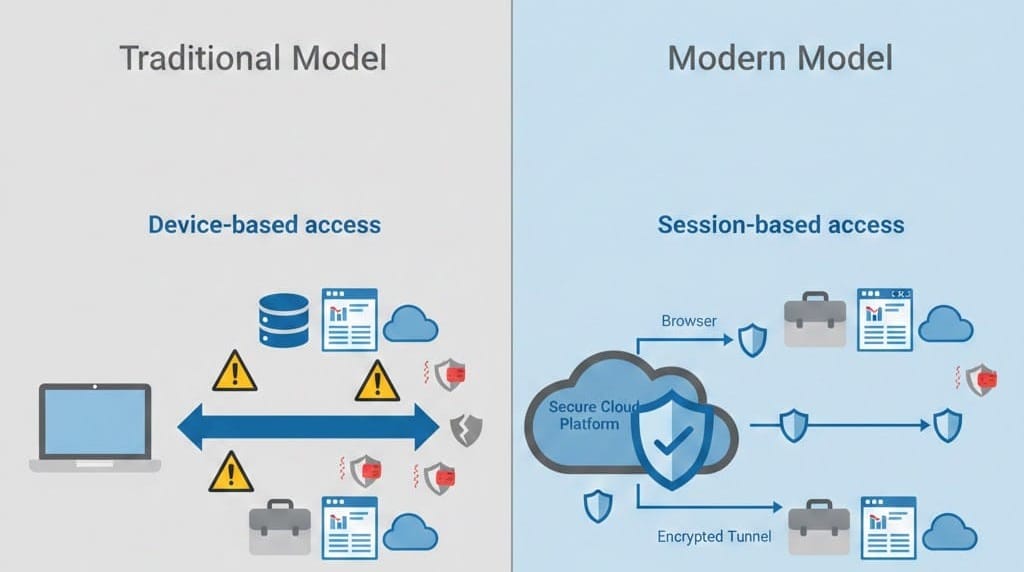
The Shift from Device Control to Session Control
Modern workforce security should not begin with hardware. It should begin with execution context.
The most effective control model for contractors is not endpoint ownership. It is session ownership.
Browser-delivered virtual desktops illustrate this transition:
- The user brings the device
- The platform provides the controlled environment
- Data remains inside cloud infrastructure
- Sessions terminate when work concludes
This architecture redefines the enterprise trust boundary.
- Contractors see pixels
- Enterprises retain data
- Policy enforcement resides in the platform
- Endpoints become disposable access surfaces
Organizations can scale workforce access without scaling physical risk.
What Changes When Compute Leaves the Laptop
When execution moves from endpoints to centralized infrastructure, several operational shifts occur.
Device capability becomes largely irrelevant.
Even older laptops function effectively because computation occurs in the cloud.
Deployment friction disappears.
- No client installation
- No VPN configuration
- No imaging cycles
Access becomes a secure link rather than a shipped device.
Security posture improves.
- No local downloads
- No endpoint data storage
- Centralized governance and enforcement
For regulated enterprises, this represents a control improvement rather than a convenience upgrade.
Why This Matters for Compliance, Not Just Speed
Speed without governance introduces risk. Governance without speed introduces operational friction.
Regulated environments require both.
A browser-based VDI architecture can enable:
- Enforced data residency
- Centralized audit logging
- Consistent access governance
- Session-level revocation
- Alignment with zero-trust security models
Because workloads and data remain inside controlled infrastructure, contractor devices never store regulated information.
This differs materially from:
- VPN plus local application environments
- Legacy VDI with heavy clients
- Hardware-bound endpoint architectures
The Cost Structure Shift Most Enterprises Miss
The financial shift is not simply hardware reduction. It is operational decoupling.
When onboarding depends on devices:
- IT becomes logistics management
- Security depends on endpoint enforcement
- Project timelines depend on shipping cycles
When onboarding depends on sessions:
- IT focuses on identity and access governance
- Security policies live in the platform
- Projects begin as soon as access is issued
Enterprises adopting browser-delivered desktops often experience:
- Faster contractor ramp-up and ramp-down
- Reduced support overhead
- Licensing aligned with usage
- Improved audit visibility
The largest advantage is optionality.
Organizations can scale workforce capacity without expanding device fleets.
The Strategic Mistake: Treating This as a Tool Choice
This transition is not about choosing another VDI product. It is about deciding where enterprise control resides.
Traditional models assume:
- Control lives on the device
- Risk resides with the user
- Access lives in the network
Modern browser-delivered architectures shift these assumptions:
- Control lives in the platform
- Risk lives in the session
- Access lives in identity
As contractor workforces grow, onboarding architecture becomes a continuity concern rather than a simple IT decision.
What Organizations That Get This Right Do Differently
Leading organizations change the question they ask.
Instead of asking:
“How fast can we ship laptops?”
They ask:
“How quickly can we provision controlled work environments?”
They measure metrics such as:
- Time to first productive hour
- Access revocation latency
- Audit visibility
- Data movement exposure
Contractors are treated as temporary execution contexts rather than temporary employees.
Why Neverinstall Was Built for This Use Case
Neverinstall was designed around a simple premise: work should not depend on hardware.
It is a cloud-native, browser-delivered virtual desktop platform built for environments where:
- Infrastructure reliability is critical
- Data residency requirements are strict
- Compliance posture defines architecture
- Vendor lock-in must be avoided
The platform enables:
- BYOD contractor environments
- Frictionless onboarding
- Centralized policy enforcement
- Data-in-cloud security
- Session-level access control
The goal is not simply remote work enablement. It is regulated access at enterprise scale.
The Real Question CIOs Should Be Asking
The strategic question is not:
“Can contractors become productive faster?”
It is:
“Why should productivity depend on hardware at all?”
Every device shipped introduces:
- Additional risk surface
- Deployment delay
- Operational overhead
Every controlled session issued preserves:
- Governance
- Speed
- Architectural flexibility
Closing Perspective
Contractors are hired to solve problems, not to wait for logistics.
If onboarding still begins with procurement and ends with tracking numbers, organizations are addressing a modern workforce challenge with a legacy control model.
The infrastructure that succeeds in regulated industries will not simply secure devices more aggressively. It will reduce the role of devices altogether.
The real question is not whether browser-delivered desktops work.
It is how long enterprises can afford to rely on laptops as the primary control point for regulated work.
